A Beginner’s Guide to Digital Forensics and Incident Response (DFIR)
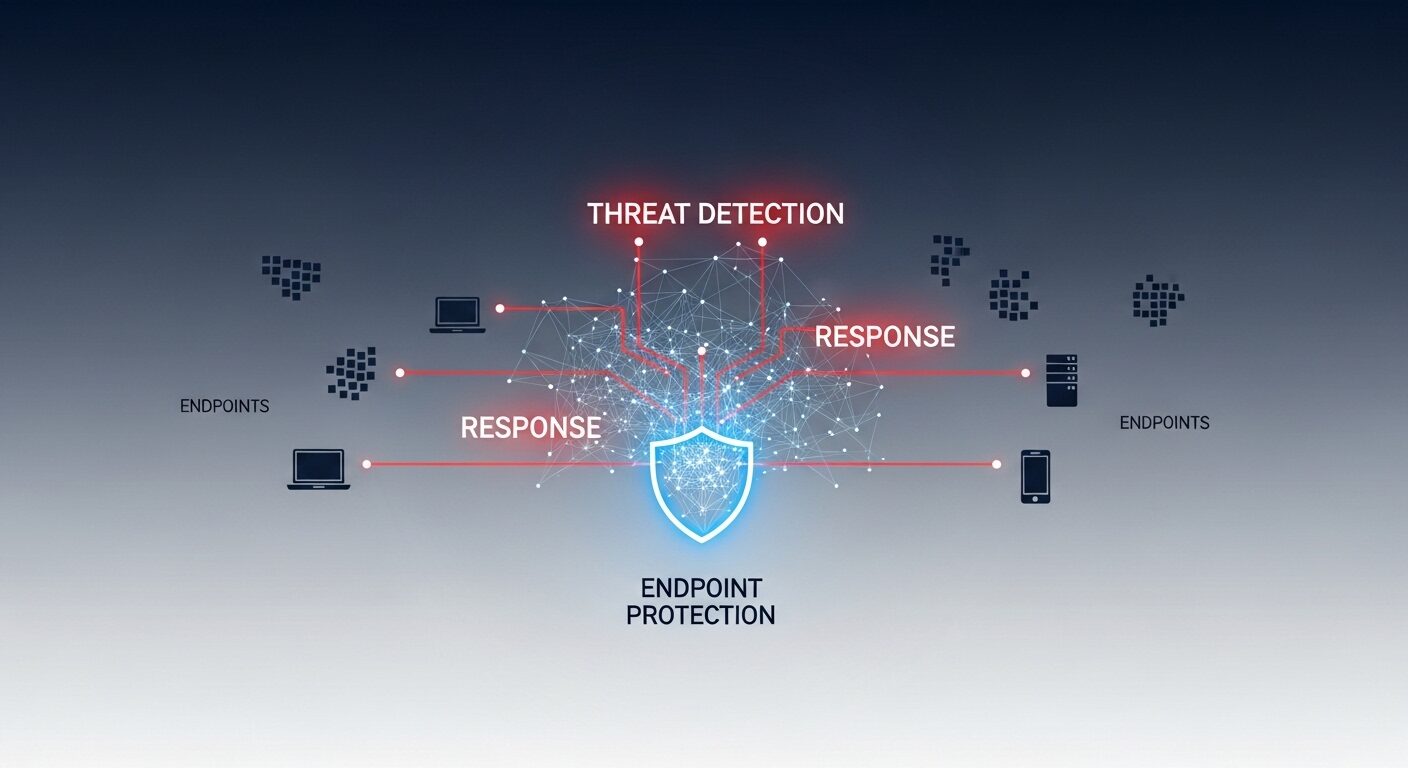
⏱ 8 min readDigital Forensics and Incident Response (DFIR) is the specialized cybersecurity discipline focused on identifying, investigating, and remediating security breaches. This DFIR beginner guide explains how professionals methodically handle cyber