⏱ 8 min read
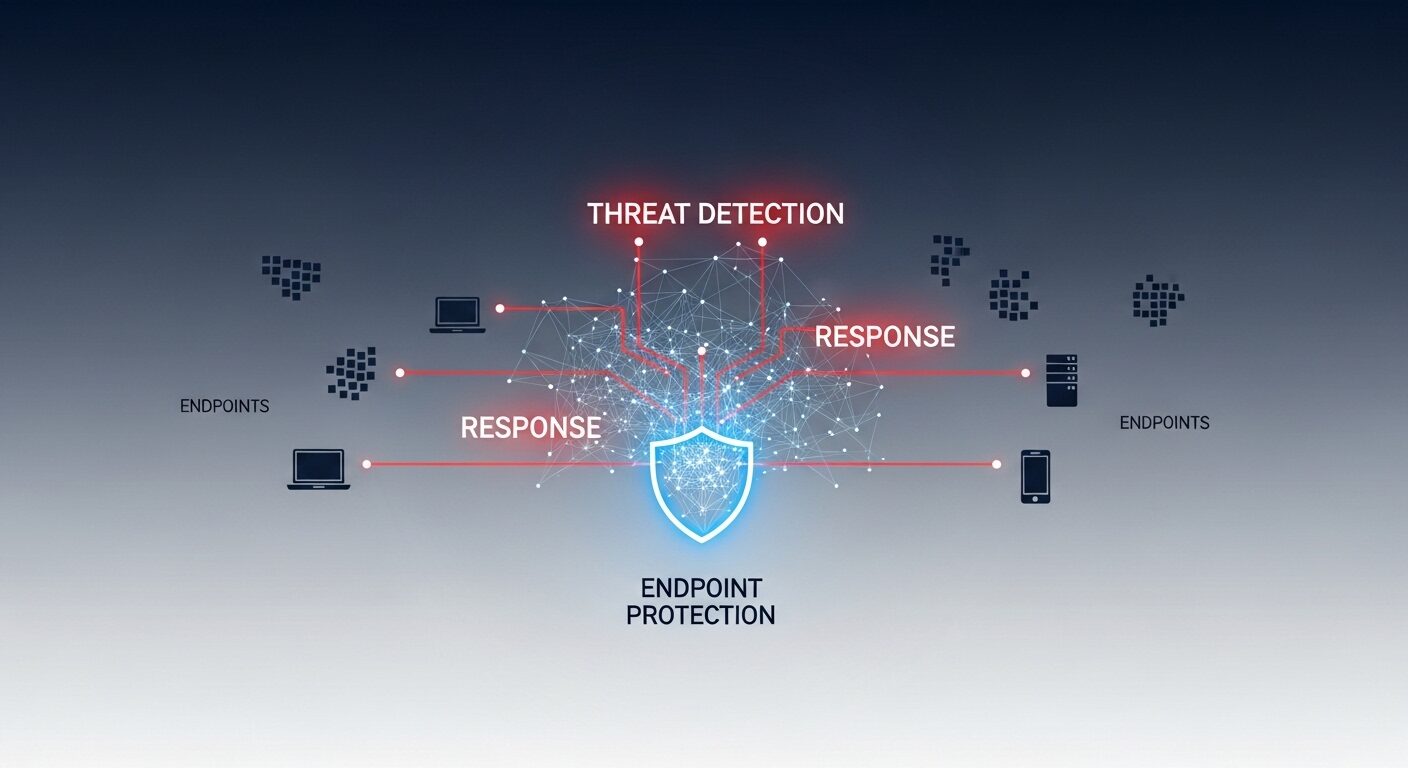
Endpoint Detection and Response, commonly called EDR, is a critical cybersecurity technology designed to protect devices like computers, servers, and mobile phones from advanced threats. It goes beyond traditional antivirus by continuously monitoring endpoint activities, using behavioral analysis to detect suspicious actions, and providing tools for security teams to investigate and contain incidents rapidly. This comprehensive guide explains the core functions, benefits, and operational processes of modern EDR platforms, which are essential for any organization’s defense against evolving cyberattacks.
Key Takeaways
- EDR provides continuous monitoring and recording of endpoint activities.
- It uses behavioral analysis to detect threats that bypass traditional antivirus.
- Core capabilities include detection, investigation, and response.
- It is a foundational component of modern security operations centers (SOCs).
- Effective EDR reduces the time to detect and respond to security incidents.
- Integration with other security tools enhances overall protection.
What is Endpoint Detection and Response (EDR)?
Endpoint Detection and Response (EDR) is a cybersecurity technology that continuously monitors and collects data from endpoint devices to identify, investigate, and mitigate suspicious activities and advanced threats. It provides security teams with visibility, detection, and response capabilities beyond traditional signature-based antivirus software.
Endpoint Detection and Response is a security solution focused on endpoints—any device that connects to a network. EDR solutions are defined by their integrated approach to threat detection, investigation, and response. The term was coined by the analyst firm Gartner in 2013 to describe tools that record endpoint activities and apply analytics to find threats. According to industry data, organizations using EDR can significantly improve their threat detection rates.
These platforms aggregate data from across all endpoints in an environment. This creates a searchable record of system processes, network connections, and user actions. Security analysts use this data for proactive threat hunting and rapid incident response. The goal is to stop attacks before they cause major damage.
How Does EDR Work to Protect Your Systems?
EDR works by deploying lightweight agents on endpoints like laptops, desktops, and servers. These agents collect vast amounts of telemetry data in real-time. The core mechanism involves continuous data collection and behavioral analysis. This data is sent to a central management console for correlation and analysis.
The system uses rules, machine learning, and threat intelligence to spot anomalies. For example, it might flag a process attempting to encrypt numerous files rapidly, indicative of ransomware. When a threat is detected, the platform alerts security personnel and can often automate initial containment steps, such as isolating the affected endpoint from the network.
Experts recommend EDR for its depth of visibility. It doesn’t just look for known malware signatures. Instead, it analyzes the behavior of files and processes. This allows it to catch novel attacks, fileless malware, and living-off-the-land techniques that use legitimate system tools for malicious purposes.
What Are the Core Capabilities of an EDR Solution?
A robust endpoint detection and response platform offers several key functions. The primary capabilities are detection, investigation, and remediation. First, it must detect threats through continuous monitoring and advanced analytics. This includes identifying malware, exploits, and suspicious user behavior.
Second, it provides deep forensic investigation tools. Security teams can search through historical data to understand an attack’s scope and origin. They can trace the attacker’s steps across the network. Third, it enables rapid response. This can involve killing malicious processes, deleting files, or isolating machines.
Additional vital features include threat intelligence integration and reporting. Many platforms, like those from CrowdStrike or Microsoft, also offer managed detection and response (MDR) services. These services provide 24/7 monitoring by external security experts, a valuable option for organizations with limited in-house staff.
EDR vs. Antivirus and Other Endpoint Security
Understanding the difference between EDR and traditional tools is crucial for building effective defenses. EDR represents an evolution from reactive, signature-based protection to proactive, behavior-focused security. Traditional antivirus software relies on a database of known malware signatures to block threats. It is largely reactive and can miss new, unknown attacks.
Endpoint detection and response solutions take a broader view. They monitor for suspicious behaviors and patterns, not just known bad files. This makes them far more effective against zero-day exploits and advanced persistent threats (APTs). The standard approach in modern cybersecurity is to use EDR alongside next-generation antivirus (NGAV) for layered protection.
How EDR Detects and Responds to an Incident: A Step-by-Step Process
- Data Collection: An agent on an endpoint continuously records system activity, including process creation, registry changes, and network connections.
- Detection & Alerting: Analytics engines analyze the collected data. Suspicious behavior, like a script accessing sensitive files, triggers an alert in the security console.
- Investigation: An analyst uses the EDR’s search and visualization tools to investigate the alert, examining the timeline and scope of the activity.
- Containment: The analyst or an automated playbook takes action to contain the threat, such as quarantining the endpoint or terminating a malicious process.
- Remediation & Reporting: The threat is fully removed, systems are restored, and a report is generated for compliance and improving future defenses.
The following table compares key aspects of EDR with traditional endpoint protection:
| Feature | Traditional Antivirus (AV) | Endpoint Detection & Response (EDR) |
|---|---|---|
| Primary Focus | Preventing known malware infections | Detecting, investigating, and responding to advanced threats |
| Detection Method | Signature-based, heuristic analysis | Behavioral analysis, machine learning, anomaly detection |
| Response Capability | Limited to quarantine/delete | Advanced containment, forensic investigation, threat hunting |
| Data Retention | Minimal or none | Extensive historical data for forensics |
| Threat Intelligence | Basic updates | Integrated global threat feeds and context |
Why is EDR Essential for Modern Cybersecurity?
EDR is essential because the threat landscape has evolved dramatically. Advanced attacks specifically target endpoints as the primary entry point into a network. Research shows that over 70% of successful breaches start at the endpoint. Attackers use sophisticated methods that easily evade basic defenses.
An endpoint protection platform with EDR capabilities provides the visibility needed to catch these attacks. It shrinks the critical “dwell time”—the period an attacker goes undetected inside a network. Reducing dwell time limits data theft and system damage. Furthermore, compliance frameworks increasingly recommend or require continuous monitoring capabilities that EDR provides.
For a robust security posture, tools like Cyber Guard integrate EDR with other systems. This creates a security ecosystem where information is shared between tools, leading to faster and more accurate threat detection across the entire IT environment.
How to Implement an EDR Strategy: A Step-by-Step Guide
Implementing EDR successfully requires careful planning and execution. A successful implementation starts with defining clear security goals and requirements. First, assess your current endpoint security posture and identify gaps. Determine which assets are most critical and need the highest level of protection.
Next, select an EDR solution that fits your technical environment and team’s skill level. Consider cloud-based versus on-premises deployment models. Then, begin a phased rollout, starting with a pilot group of non-critical endpoints. This allows you to tune detection rules and minimize false positives before full deployment.
Finally, ensure your security team is trained to use the investigation and response tools effectively. Integrate the EDR platform with your existing security information and event management (SIEM) system and other security tools. Continuously review alerts and refine your processes to improve over time.
Frequently Asked Questions
What is the main purpose of EDR?
The main purpose of Endpoint Detection and Response is to provide continuous monitoring, advanced threat detection, and rapid response capabilities for endpoint devices. It helps security teams identify malicious activity that bypasses other defenses, investigate the full scope of an incident, and take action to contain and eliminate threats.
How is EDR different from XDR?
EDR focuses specifically on security for endpoints like computers and servers. XDR, or Extended Detection and Response, expands this visibility by integrating and correlating data from endpoints, networks, cloud workloads, and email. XDR provides a more unified view across multiple security layers for improved detection and faster investigation.
Can EDR replace antivirus software?
Most experts recommend using EDR alongside next-generation antivirus (NGAV), not as a complete replacement. 85% of organizations use EDR to augment their existing endpoint protection. NGAV handles widespread, known malware efficiently, while EDR targets sophisticated, stealthy attacks, creating a more robust defense-in-depth strategy.
What are the common challenges with EDR?
Common challenges include managing alert fatigue from false positives, the need for skilled analysts to interpret data, and the resource requirements for storing large volumes of endpoint telemetry data. Successful deployment requires proper tuning of detection rules and often benefits from integration with a Security Operations Center (SOC).
Is EDR suitable for small businesses?
Yes, EDR is suitable for businesses of all sizes. Many vendors now offer cloud-based EDR solutions that are scalable and manageable for smaller teams with limited IT security staff. Some providers also offer Managed Detection and Response (MDR) services, where